by Gary Mintchell | Nov 1, 2019 | Manufacturing IT, Security
Internet of Things installations along with industrial control systems constitute well known cybersecurity vulnerabilities within industrial plants and operations. CyberX, the IoT and industrial control system (ICS) security company, announced the availability of its “2020 Global IoT/ICS Risk Report” designed to sharpen awareness and knowledge of this critical area.
The data illustrates that IoT/ICS networks and unmanaged devices are soft targets for adversaries, increasing the risk of costly downtime, catastrophic safety and environmental incidents, and theft of sensitive intellectual property.
Some of the top findings noted that these networks have outdated operating systems (71 percent of sites), use unencrypted passwords (64 percent) and lack automatic antivirus updates (66 percent).
Energy utilities and oil and gas firms, which are generally subject to stricter regulations, fared better than other sectors such as manufacturing, chemicals, pharmaceuticals, mining, transportation and building management systems (CCTV, HVAC, etc.).
Now in its third year, CyberX’s “Global IoT/ICS Risk Report” is based on analyzing real-world traffic from more than 1,800 production IoT/ICS networks across a range of sectors worldwide, making it a more accurate snapshot of the current state of IoT/ICS security than survey-based studies.
Including the data presented in previous reports, CyberX has now analyzed over 3,000 IoT/ICS networks worldwide using its patented M2M-aware behavioral analytics and non-invasive agentless monitoring technology.
Recommendations Focus on Prioritization and Compensating Controls
The report concludes with a practical seven step process for mitigating IoT/ICS cyber risk based on recommendations developed by NIST and Idaho National Labs (INL), a global authority on critical infrastructure and ICS security.
Experts agree that organizations can’t fully prevent determined attackers from compromising their networks. As a result, they recommend prioritizing vulnerability remediation for “crown jewel” assets — critical assets whose compromise would cause a major revenue or safety impact — while implementing compensating controls such as continuous monitoring and behavioral anomaly detection (BAD) to quickly spot intruders before they can cause real damage to operations.
“Our goal is to bring board-level awareness of the risk posed by easily-exploited vulnerabilities in IoT/ICS networks and unmanaged devices — along with practical recommendations about how to reduce it,” said Omer Schneider, CyberX CEO and co-founder.
“Today’s adversaries — ranging from nation-states to cybercriminals and hacktivists — are highly motivated and capable of compromising our most critical operational systems,” said Nir Giller, CyberX GM, CTO and co-founder. “It’s now incumbent on boards and management teams to recognize the risk and ensure appropriate security and governance processes are in place across all their facilities to address it.”
Summary of Key Findings
- Broken Windows: Outdated Operating Systems. 62 percent of sites have unsupported Microsoft Windows boxes such as Windows XP and Windows 2000 that no longer receive regular security patches from Microsoft, making them especially vulnerable to ransomware and destructive malware. The figure rises to 71 percent with Windows 7 included, which reaches end-of-support status in January 2020.
- Hiding in Plain Sight: Unencrypted Passwords. 64 percent of sites have unencrypted passwords traversing their networks, making it easy for adversaries to compromise additional systems simply by sniffing the network traffic.
- Excessive Access: Remotely Accessible Devices. 54 percent of sites have devices that can be remotely accessed using standard management protocols such as RDP, SSH and VNC, enabling attackers to pivot undetected from initial footholds to other critical assets. For example, during the TRITON attack on the safety systems in a petrochemical facility, the adversary leveraged RDP to pivot from the IT network to the OT network in order to deploy its targeted zero-day malware.
- Clear and Present Danger: Indicators of Threats. 22 percent of sites exhibited indicators of threats, including suspicious activity such as scan traffic, malicious DNS queries, abnormal HTTP headers, excessive number of connections between devices and malware such as LockerGoga and EternalBlue.
- Not Minding the Gap: Direct Internet Connections. 27 percent of sites analyzed have a direct connection to the internet. Security professionals and bad actors alike know that it takes only one internet-connected device to provide a gateway into IoT/ICS networks for malware and targeted attacks, enabling the subsequent compromise of many more systems across the enterprise.
- Stale Signatures: No Automatic Antivirus Updates: 66 percent of sites are not automatically updating Windows systems with the latest antivirus definitions. Antivirus is the very first layer of defense against known malware — and the lack of antivirus is one reason why CyberX routinely finds older malware such as WannaCry and Conficker in IoT/ICS networks.

by Gary Mintchell | Sep 27, 2019 | Internet of Things, Productivity
Presentations abound at Emerson Global Users Exchange. Attendees can choose to take deep technical dives into Emerson products, get overviews and trends of technology and the industry, and even personal development. Yes, there was even a 6 am fitness time with either running or Yoga.
Where’s “The Edge”? Yes, you can use good presentation skills for career success. Building Your Personal Brand through Digital Transformation–or social media an networking. Here’s a recap of the 2019 Emerson Global Users Exchange based upon several sessions I attended led by people I’ve known for a long time–Dave Imming, Mike Boudreaux, and Jim Cahill.
The Secure First Mile–IIoT and the Edge
A panel discussion assembled and led by Emerson’s Director of Connected Plant Mike Boudreaux, discussed Industrial Internet of Things in relation to “Where is the Edge”. The blend of IT and OT on the panel was refreshing and informative. Most instructive was how far each has come toward understanding the entire picture broadening from each’s silos.
Attila Fazekas, ExxonMobil, stated that IoT connects to Level 4 of the Purdue model. He is part of the IT organization taking the view from that side of the divide. He noted that his company tries to have a hard line between the IoT (IT) and control systems, although he admitted that occasionally the line becomes blurred. He was a strong proponent of IT governance, notes they have a hard line between IoT and control system (although in effect the line sometimes gets a bit smudged).
Peter Zornio, CTO Emerson Automation, relates IoT and Edge to “a giant SCADA system.” He reflects those who come from the plant where intelligent devices are connected to an automation system, which formerly was the single point where data was collected and then passed through. I have talked with Zornio for years. Few people in the industry are as knowledgeable about the plant. He is beginning to adjust to the IT world with which he’s going to have to work in the future. Especially given Emerson’s expanded strategy into digital transformation and “Top Quartile Performance.” He sees security helping drive Edge applications to divide systems providing a firm break between control systems and IT systems.
Jose Valle, CTO Energy/Manufacturing at MIcrosoft, brought another IT view to the panel. For him, The Edge becomes a place for security with a separation of functions. He also brought an emphasis on provisioning devices through the cloud.
Rich Carpenter, Executive Product Manager, Emerson Automation / Machinery (former CTO of GE Fanuc/GE Intelligent Platforms), discussed a new Edge computer from Emerson (GE). It uses Hypervisor to run RTOS and PLC control on part of chip segmented by firewall from regular PC chip running Linux for IoT functions. Noted that for the latter, they’ve discovered it better to use Node-RED and Python for programming. Congratulations to Rich for landing at Emerson—he’s another long-time contact. And thanks for mentioning Node-RED.
Overall, the panel expressed concerns about providing security with the IIoT and Edge devices. The best part was Boudreaux’s assembling a panel split evenly with IT and OT and there was no acrimony or “you think this, we think that” nonsense. They are all trying to solve bigger problems than just IT or OT only. Businesses are driving them together to solve “digital transformation” challenges. Good stuff.

by Gary Mintchell | Jul 25, 2019 | Commentary, News, Security
The International Society of Automation (ISA) held a press conference today to announce the first Founding Members of its new Global Cybersecurity Alliance (GCA): Schneider Electric, Rockwell Automation, Honeywell, Johnson Controls, Claroty, and Nozomi Networks.
As we would expect, the speakers emphasized the importance of standards as the foundation for work in the Alliance. Speakers also tied in safety and productivity as partners with cybersecurity in protecting and improving manufacturing and critical infrastructure facilities and processes. I’m not so sure just exactly what the Alliance will accomplish, but if it succeeds in just raising awareness and a sense of urgency among companies it the industries, it will have accomplished an important task.
ISA created the Global Cybersecurity Alliance to advance cybersecurity readiness and awareness in manufacturing and critical infrastructure facilities and processes. The Alliance brings end-user companies, automation and control systems providers, IT infrastructure providers, services providers, and system integrators and other cybersecurity stakeholder organizations together to proactively address growing threats.
ISA is the developer of the ANSI/ISA 62443 series of automation and control systems cybersecurity standards, which have been adopted by the International Electrotechnical Commission as IEC 62443 and endorsed by the United Nations. The standards define requirements and procedures for implementing electronically secure automation and industrial control systems and security practices and assessing electronic security performance. The standards approach the cybersecurity challenge in a holistic way, bridging the gap between operations and information technology.
Leveraging the ISA/IEC 62443 standards, the Global Cybersecurity Alliance will work to increase awareness and expertise, openly share knowledge and information, and develop best practice tools to help companies navigate the entire lifecycle of cybersecurity protection. The Alliance will work closely with government agencies, regulatory bodies, and stakeholder organizations around the world.
“Accelerating and expanding globally relevant standards, certification, and education programs will increase workforce competence, and help end users identify gaps, reduce risks, and ensure they have the tools and systems they need to protect their facilities and installations,” said Mary Ramsey, ISA Executive Director. “Through the proliferation of standards and compliance programs, we will strengthen our global cyber culture and transform the way industry identifies and manages cybersecurity threats and vulnerabilities to their operations.”
The press release notes that first Founding Members of the Alliance are leading multi-national, industrial-technology providers with deep expertise in technology and applications, and they’ll apply their experience and knowledge to accomplish the Alliance’s priorities. However, two of the members were represented by building automation divisions. Two of the members are cybersecurity suppliers. Rockwell Automation is a pure play factory and process automation company and its Maverick Technologies division has been an ardent supporter of ISA. Schneider Electric is a large, multi-disciplined company, and I’m not sure which division within it is the sponsor.
“Participating in the Alliance truly shows the commitment our founding members have to the safety and security of the industrial ecosystem, as well as the criticality of collectively moving forward together to ensure the standards, best practices and methods are applied,” Ramsey said.
“ISA engaged with discussions, initiated by Schneider Electric, to create an ISA-led global, open and industry-wide alliance comprised of all cybersecurity stakeholder companies. ISA quickly expanded those conversations to include Rockwell Automation, Honeywell, Johnson Controls, Claroty, and Nozomi Networks. These first Founding Members have since worked together to help us define the Alliance’s objectives. We are thankful for their collaboration and commitment. Together we welcome companies and organizations from all segments of industry to join our efforts.”
The Alliance is seeking additional members to support its initiatives. End-user companies, asset owners, automation and control systems providers, IT infrastructure providers, services providers, and system integrators and other cybersecurity stakeholder organizations are invited to join. Annual contributions to fund initiatives are based on company revenues and are tax-deductible.
Perspectives: Quotes from the ISA Global Cybersecurity Alliance Founding Members
“Over the last few years, global industry has recognized that taking on increasingly dangerous cyber risks can’t be limited to a single company, segment, or region. However, until now, there has been limited ability to respond as a unified whole to these worldwide threats. But by establishing an open, collaborative, and transparent body, with a focus on strengthening people, processes, and technology, we can drive true cultural change. We are pleased that ISA has stepped forward, and we look forward to working openly and collaboratively with them, our fellow Founding Members, and many others affiliated with global industry, especially end users. Together we will bring to bear the standards-based technology, expertise, and special skills required to better secure and protect the world’s most critical operations and the people and communities we serve.” — Klaus Jaeckle, Chief Product Security Officer, Schneider Electric
“Cybersecurity is critical to digital transformation. It’s critical not only for the protection of information and intellectual property, but also for the protection of physical assets, the environment, and worker safety. We make it a priority to collaborate with partners and research institutions to develop secure products. Rockwell Automation participated in the development of the 62443 standards from the beginning and continues to support ISA cybersecurity initiatives. Our engagement with the Global Cybersecurity Alliance will be another important step in our efforts to help customers identify and mitigate risks.” — Blake Moret, CEO, Rockwell Automation
“Cybersecurity is the great equalizer to all companies. It’s critical to the connected world we live in and the cornerstone of trust that the world needs to be able to operate. Whether protecting critical infrastructure or managing a building’s operations, users need to do this with the confidence the employed systems are robust and secure. We are committed to and proud to work together ISA and the GCA members to continue to drive the adoption of the ISA/IEC 62443 series of standards and identify further ways to secure and protect the connected world which we live. At Honeywell, we see cybersecurity as a core part of the future we are making, and we see the GCA as an important way to work together to make that happen.” — Matthew Bohne, Vice President and Chief of Product Security, Honeywell Building Technologies
“Digital transformation in the building sector continues to accelerate, which heightens the urgency for cybersecurity across the industry and beyond. As a leader in the industrial automation controls business, Johnson Controls is already a strategic member of the ISASecure program and is consistently taking proactive actions to protect customers against cyber-threats and risks. Joining ISA Global Cybersecurity Alliance is a necessary and meaningful step as it supports our company values, customer adoption of the ISA/IEC 62443 standard and efforts to educate global government and regulatory bodies. We are proud to solidify our commitment to this important effort.” — Jason Christman, Vice President, Chief Product Security Officer, Global Products, Johnson Controls
“One of the most effective ways to drive consistency in an industry is by putting standards in place, and we’re looking forward to collaborating with all of these founding members, as well as future Alliance members, to help drive global best-practices forward in this historically standard-less environment. Claroty is committed to the mission of protecting all IoT and OT networks from cyber risks. Through our work with the Global Cybersecurity Alliance, we will be able to help shape the future of cybersecurity in these high-risk industries.” — Dave Weinstein, Chief Security Officer, Claroty
“Nozomi Networks believes real community collaboration, actionable standards and effective education are key ensuring a secure future for industrial organizations around the world. That’s why we are helping develop secure-by-design standards as a working member of ISA99 standards committees, why we’ve designed our industrial cyber security solutions for easy integration across the broadest possible set of industrial and IT technologies; and why we are thrilled to help establish the Global Cybersecurity Alliance. Together we will build a secure future for the industrial infrastructure that runs the world.” — Andrea Carcano, Nozomi Networks Co-founder and Chief Product Officer

by Gary Mintchell | Aug 8, 2018 | Automation, Process Control, Technology
Foxboro and Triconex looks to be on the path to health under Schneider Electric. Its annual user conference is this week in San Antonio. I‘d love to be there, but personally more important is “grandparent duty” that I’m on this week. So, I had the opportunity to talk with Gary Freburger, leader of the group, and Peter Martin, VP of marketing, to get an update and view of what I’ll be missing.
Gary Freburger began with the market rebounding due to current oil pricing. Business is starting to get strong. IA product line has done well and the process business also did well going up 6% in the first half of the year. He’s expecting majority of growth over the next two years. Schneider Electric is still investing around EcoStruxure system. Foxboro is continuing on the path they discussed with us at the last user conference—how to get more value from control systems going from “necessary evil” to value add in the eyes of customer executives. The strategy is to turn data and connectivity into a business driver. The goal is enabling better decisions and improving profitability.
Freburger discussed cooperating with OPAF for a comprehensive strategy. Then he dropped in an interesting tidbit—cooperation with AVEVA. I’ve wondered about how AVEVA with the inclusion of previous Schneider Electric software would work with the Foxboro side of things. He told me they now have and end-to-end relationship to improve time to market. He noted as oil prices dropped customers thought “what can I afford to do?” Now, all have reset expectations. As oil prices rebound, they have not changed expectations. Some interesting applications and strategies include AVEVA auto populate control system, digital twin of facility, operations feedback our systems to AVEVA’s, then customer asset management upgrade works easier.
Martin discussed how Schneider is trying to change the question—from how to do control to how do we help customers solve problems that impact business? He pointed out that they’ve been doing digitization for years. What’s new is how to drive this new approach. 40 years ago controls was a solution-driven business; then with digitization the industry went from solutions to technology-driven. The times now require a need to flip flop. Solutions oriented but with today’s portfolios taking it to a much higher level. The speed of industrial business has increased—what was stable, e.g. cost of electricity—is stable no longer. The speed means IT world can’t keep up. Built-in real-time accounting control helps plants go beyond control to profitability. Foxboro is still dedicated to taking the use of technology to the next level.
During the conference (while I am writing from the forests in southern Ohio while the grandkids are in bed), Schneider Electric announced the release of EcoStruxure Foxboro DCS Control Software 7.1.With expanded capabilities and an enhanced HMI, the updated software simplifies engineering and enhances the user experience, while expanding the ability of EcoStruxure Foxboro DCS to drive measurable operational profitability improvements, safely.
The EcoStruxure Foxboro DCS is an open, interoperable and future-proof process automation system that provides highly accurate and effective control over a manufacturing plant’s operational profitability. It is the only process control system that provides measurable operational profitability improvements and a future-proof architecture, enabling a measurable 100 percent ROI in less than one year.
EcoStruxure is Schneider Electric’s open, interoperable, IoT-enabled system architecture and platform. This includes Connected Products, Edge Control, and Apps, Analytics and Services. EcoStruxure has been deployed in 480,000+ sites, with the support of 20,000+ system integrators and developers, connecting over 1.6 million assets under management through 40+ digital services.
EcoStruxure Foxboro DCS Control Software 7.1 runs on Windows 10 and Windows Server 2016, to provide maximum flexibility while ensuring robust cybersecurity. When planning upgrades, Schneider Electric customers can mix Windows XP, Windows 7 and Windows 10 on the same system, allowing flexibility in scheduling and timing for upgrades. Customers can upgrade individual sections of the plant in any order, at any pace, to best accommodate plant production schedules. With Microsoft support for Windows 7 due to end in 2020, transitioning to Windows 10 allows EcoStruxure Foxboro DCS customers to benefit from the strongest operating system with the most up-to-date cybersecurity features.
Among other new and updated features, the continuously current EcoStruxure Foxboro DCS Control Software 7.1 now includes:
• EcoStruxure Field Device Expert that improves efficiency, safety and profitability, while considerably reducing time for startup and restarts. It includes:
◦ Intelligent Commissioning Wizard, to reduce commissioning time up to 75 percent by automating HART device commissioning and documentation processes.
◦ Device Replacement Wizard to significantly reduce time and expertise to replace or commission HART devices, either individually or in bulk.
◦ Bundled HART DD library for increased security, faster device deployment, eradication of version mismatch and elimination of cybersecurity risks previously created by moving documents from the HART consortium web page into the system.
• New HMI Bulk Graphics Editor for increased operational efficiency and reliability by greatly reducing engineering hours and improving quality during testing. Use in major projects shows that replicating hundreds of displays with the new Bulk Graphics Editor saves months of man hours and improves quality by delivering highly predictable results. The Bulk Graphics Editor makes migrating from the classic FoxView HMI to the new Foxboro DCS Control HMI easier, requiring far fewer engineering hours, which reduces the time and cost to transition between technologies.
• Control Editors Activity Monitor for increased efficiency by improving communication, workflow and collaboration.
• Real-time asset health condition monitoring for increased reliability.
• Future-proof technology supporting the latest FTD 2.0 standard, which improves compatibility with digitized field devices from Schneider Electric and third-party vendors.
• New migration path, along with the new HMI Bulk Graphics Editor, simplifies the transition from existing FoxView HMI displays to the EcoStruxure Foxboro DCS Control Software 7.1 HMI platform for a continuously current and future-proof system. An upgrade migration path is available from previous Control Software Versions 5.x, 6.x and 7.0. After upgrading, users can tap into newer technologies that improve productivity, cybersecurity, efficiency and profitability.
by Gary Mintchell | Feb 20, 2018 | Automation, Industrial Computers, Security
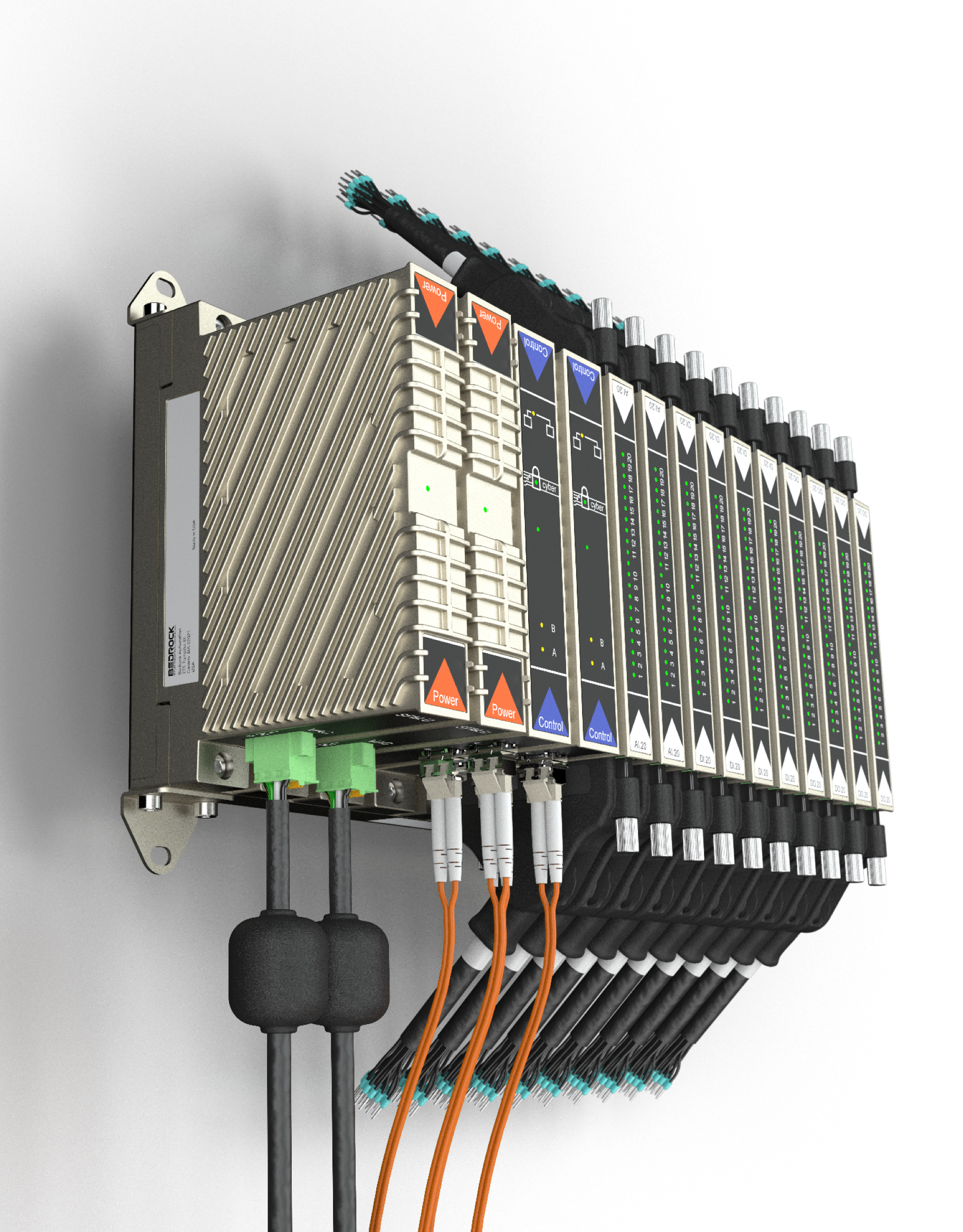
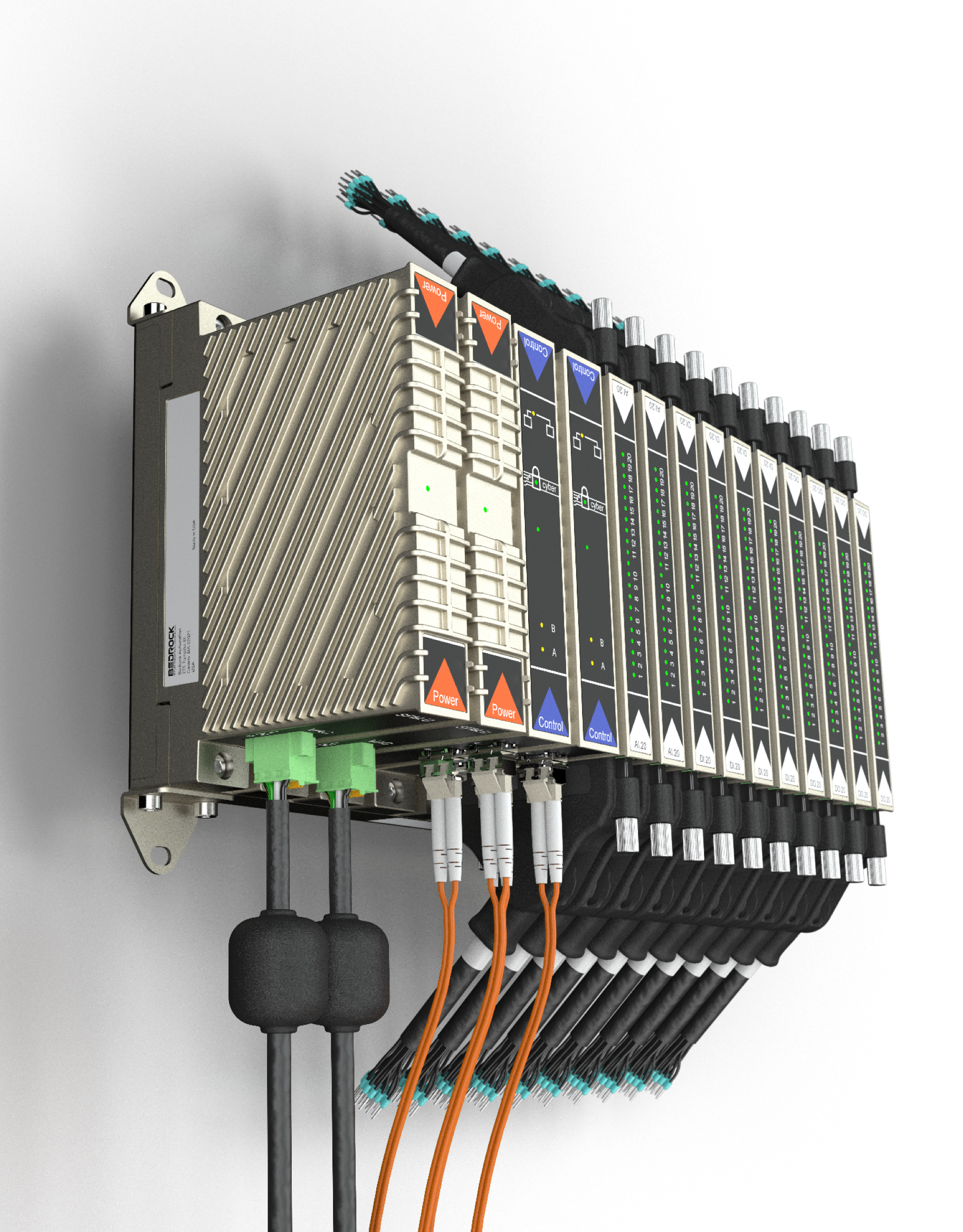
Bedrock Automation, products built for security from the chips up, had a flurry of activity at the ARC Industry Forum in Orlando last week. It announced a firmware upgrade, OPC UA and partnerships for its SCADA product, and anomaly detection. Here’s a teaser—CEO and Founder Albert Rooyakkers pulled out a new piece of hardware. He didn’t have a release or specs for me, but watch for a new, lower cost, SCADA or gateway device hardened and built with security in mind from the chips up.
Bedrock and OPC UA
Bedrock Automation has published a concise, easy-to-deploy interface specification that enables users and application developers to take advantage of the security capabilities of OPC UA communications software. By following the simple procedures outlined in the Bedrock SCADA Security Platform Specification, developers can upgrade any OPC UA compliant client into a highly secure OPC UA channel, across which users can exchange data between plant floor operations and SCADA applications. Three leading SCADA software developers, Inductive Automation, ICONICS and TATSOFT, are committing and releasing support to the Bedrock interface specification.
“OPC UA provides unique cyber security advantages enabling open communications across numerous industrial devices and applications and providing the end-users options for integrating authentication keys protecting those communications. The most secure OPC level is to authenticate those keys against a known root of trust, which Bedrock supplies via a certificate authority (CA), validated against cryptographic keys built into its controller,” said Thomas J. Burke, OPC Foundation President and Executive Director, adding “Bedrock Automation is a clear leader in supporting the OPC UA standards, and provides information integration and communication that the end users have been demanding.
Bedrock designs and sources its own secure semiconductor components with encryption and authentication technologies embedded at the “birth” of their modules, assembled and tested by Bedrock in their cyber secure supply chain. The unique design then draws on the power and flexibility of public key infrastructure (PKI) and Transport Layer Security (TLS) standards similar to those used to secure ecommerce transactions and military and aerospace electronics. Bedrock Automation then uses those securely embedded keys as the basis for digital certificates that manage access and communication between SCADA applications and control systems. Bedrock Cybershield 3.0 firmware is the first control system to offer an embedded PKI for SCADA applications.
“Such a simple specification demonstrates that Open and Secure SCADA can be deployed today, and that an applications interface does not have to be thousands or even hundreds of pages. We are pleased to be working with innovative SCADA software providers such as Inductive Automation, ICONICS and TATSOFT, to help them and their customers take advantage of the secure communications capabilities of OPC UA and the intrinsic security of the Bedrock platform,” said Rooyakkers.
Cybershield 3.0
Bedrock Automation also announced the availability of Cybershield 3.0, a major firmware upgrade with advancements that make it easier for end users and developers to build control applications that are both open and secure. Among the six major innovations facilitated by the Cybershield 3.0 upgrade are the first public key infrastructure (PKI) built into an OPC UA server for SCADA applications; an industrial Certificate Authority (CA) for user key management; virtual crypto key locks for the controller; and a Secure Proxy server capability that can protect legacy controls systems of other vendors.
“Cybershield 3.0 is one of the most significant steps forward since the release of our Bedrock OSA platform. We now support leading SCADA companies in integrating their OPC UA client to our open security and key management tools. In addition, we start our march to converge IT cyber detection technologies into real-time OT automation with our integrated Anomaly Detection (AD) tools built into every controller. We are delivering secure SCADA and AD as intrinsic and zero-cost advancements, focused acutely on ease of use and reductions in lifecycle costs,” said Bedrock founder and CEO Albert Rooyakkers.
Bedrock Cybershield 3.0 includes the following capabilities:
1) Secure Open SCADA with OPC UA. The cryptographic keys built into all the Bedrock system electronics, provide the root of trust for the Bedrock Certificate Authority (CA) that verifies the reliability of OPC UA-managed communications between SCADA and PLCs or other industrial control systems.
2) Open Certificate Authority (CA) for SCADA. This advanced SaaS key and certificate management tool is not only FREE to our customers but is simple to deploy with our Secure SCADA Interface Specification. Leading SCADA providers, including Inductive Automation, ICONICS and Tatsoft, are committing to and releasing support to this interface specification.
3) Intrusion detection. Even though the Bedrock control system has protection built into its core, users still need to know when system security is challenged. Cybershield 3.0 comes standard with intrinsic Anomaly Detection (AD) functionality that continuously monitors the controller’s network and system time to detect intrusions and anomalous behavior and report it to both SCADA and enterprise database applications for trending, alarming and historizing anomalous cyber activity.
4) Quickly Secure Legacy Automation with Secure SCADA. Companies can now use Bedrock security to help integrate open standard communications protocols with legacy PLC and DCS systems from other vendors. A Bedrock secure controller module acts as a gateway between SCADA platform workstation and the legacy controllers.
5) Cryptographic key locking. Cybershield 3.0 also includes a cryptographic controller engineering key lock that permits only users with the required credentials to change the mode of the controller.
6) Achilles and EMP compliance on power supplies. Bedrock Automation is certifying its standalone power supply and standalone uninterruptible lithium power supply to both MiL-STD-461-G, the military standard for advanced EMP hardening, and Achilles Level 2 certification, augmenting the EMP and Achilles certification achieved for its control system modules last year.
“Today’s increasingly connected environment drives the process industries to search for automation solutions that deliver the benefits of open communications with ‘baked in’ cybersecurity. By extending its secure automation technology to third-party software providers, Bedrock Automation addresses this key pain point of future automation requirements. ARC believes the intrinsic and no-cost approach of Bedrock’s cybersecurity strategy is the quintessential component missing in control systems, today,” writes ARC analyst Mark Sen Gupta in his recent report, Bedrock Automation’s Open Secure Automation a “Win” with End Users
Anomaly Detection
Bedrock Open Secure Automation (OSATM) firmware will include intrinsic Anomaly Detection (AD). Bedrock OSA AD will be available as standard integrated functionality that continuously monitors the controller’s network and system time to detect intrusions and anomalous behavior.
“Preventing control system intrusion is fundamental to holistic cyber security. In addition, users need to know when the system security is being challenged. This is the role of anomaly detection. At no additional cost or complexity for the user, Bedrock’s AD delivers additional assurance that no one is tampering with your automation,” said Rooyakkers. Bedrock Anomaly Detection includes the following functionality:
• Dynamic Port Connection Monitoring, which records all attempts to connect any controller or communication point and captures identifying information on the intruder
• Network Port Scanning, which detects if hackers are scanning for open ports that might provide access to the control network
• System Time Monitoring, which detects attepts to manipulate log files to conceal malicious activity
• Cryptographic Controller Engineering Key Lock, which permits only users with valid user credentials to change the configuration and operation mode of the controller and records all access
• Intrusion Event Logging, which records all detected anomalies and reports them to SCADA software through OPC UA and standard database access for historian, alarming, and trending functions. Additionally, a tri-color status LED on the faceplate of Bedrock Controllers provides indication locally whenever an intrusion is detected.